Recently Brovary patrol police Department detained a group of swindlers who demanded the 83-year-old woman the money. The attackers called her, introduced themselves as law enforcement officers and stated that her grandson’s car knocked down a child. To release him from criminal responsibility, asked for a thousand dollars. The woman agreed to pay, but then called the police. The criminals were detained. However, not everyone knows how to behave in such situations. Moreover, hackers constantly invent new ways to fraudulently steal money, using a thing that almost everyone has a mobile phone.
“Your son got in trouble”
This method of fraud is based on psychological pressure. Victims call on mobile or landline phone and tell the story that their loved one was in trouble or had committed a crime. To quickly allegedly to help him to avoid responsibility, ask for money. Often information is impersonal scammers do not call names, use the words “son”, “daughter” or “grandson”, but this is enough. The emphasis is on the surprise effect (late/early call) and psychological pressure – the money to be transmitted or transferred very quickly. In such a situation, many don’t even think to call a relative to see if he’s well.
If you receive such a call, first of all do not panic, ask the caller additional questions and do not call personal information. Try immediately to call the relative in question. If his phone is turned off, and the scammers keep calling every minute to rush and intimidate you, ask them to hand the phone to your relative. They won’t be able to do, and you make sure that you call scams.
As recommended by law enforcement, if you received such a call, do not hurry to refuse the scams. Ask them to call back while they call the police. This will help the police to catch them.
Smiling
Smishing is a type already known to Internet users of phishing. The goal of phishing is to gain access to sensitive user data – usernames and passwords. For example, this can be done by sending out from well-known brands, banking services or using social networks. Phishing emails contain a direct link, clicking on which takes the user to a fake website (it looks almost identical really). The purpose of the Scam is to force the user to enter on this website the username and password from the present. If he did, his data fall into the wrong hands.
In the case of smishing with this aim used SMS. The message is a link to a phishing site. Still, for example, the victim can offer to send may look like a SMS from a Bank or well-known companies. For example, in Ukraine recently mass messages were sent on behalf of the banks stating that a card or account user that something is wrong. To resolve issues had to call back to the specified message to the phone. If trusting the user call back – scammers on the other end trying to ferret out confidential information.

To avoid this situation, you need to remember to call the Bank it is possible only those numbers that are listed on the back of the card. Moreover, staff will find out from the PIN, CVV codes (three digits on the back of the card), card expiry date, and the username and password to access online banking. Name, complete card number and password used by Bank employees to identify only when you turn to him in official phones.
If you get a call supposedly from Bank staff and are asked to identify, confirm the data, for example, the word password, or personal information, do not continue this conversation. If you talked to the fraud and fear that could tell a secret data – just call the contact centre of Bank and block your card.
Another option smishing is a message about the unexpected win. For example, a car. SMS can be a link to a phishing site. But even if it is not, and the user believe in his good luck, he will try to pull the money, for example, under the pretext that the act winnings are taxed, and this amount you need to pay to get it.
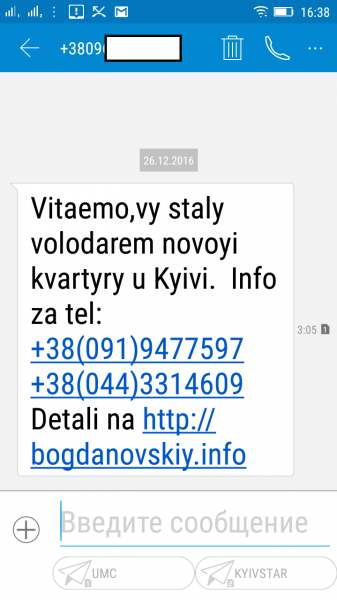
In order not to fall into the trap, remember no one gives out prizes just. Such messages do not need any to answer, nor call back the numbers or follow the links in them. If, however, didn’t disclose any information of a personal nature and do not list anyone money.
Attempts to make a copy of the SIM
The modern user most banking services, social networks, email accounts, etc. connected to the SIM card of the mobile phone. For fraud is a wide field for fraud. Primarily in the field of risk provided by payment systems, although access to them is not easy.
So, there is a way to get a SIM card from another user: to block and to reissue it. To do this, the scammers start with the different rooms to carry out short calls to the phone of the card owner. Seeing missed calls, calls back the user, but to call anyone on the other end of the line fails. Further in his account has received a Deposit, and after that, the card stops working. This is because scammers appeal to the operator to recover alleged lost or stolen card. One of the ways to confirm that the card belongs to you, to call several numbers to which calls were made in recent years, and the amount of the last refill. After the SIM card was in the hands of criminals, all of your service messages and access to resources come to it.
It carries some risk for those whose SIM card was tied to your debit card. Having access to mobile, hackers can find a way to get to online banking, especially if they have the card number (for example, you sold something on some trading platform, providing the transaction card number of the buyer). Moreover, some banks have the ability to withdraw money from ATM without card, having on hand only the number and the phone attached to it.
To avoid such problems, should not be tied to the map, the phone number that you use daily. Also, do not divulge (especially the Internet), a telephone number, which is assigned to Bank cards.
In addition, you should pay more attention to who is calling you, and don’t rush to call back – if you really want to communicate, after the third ring the phone is either not quit, or back again. But the most reliable to date way to protect the SIM card – contract service where your phone is registered on your passport details.
Recall that the NBU told about how to behave during the attempted theft of payment card data, with external interactive voice response (IVR). In this scheme, the cardholders did not call themselves fraud, and programmed their robots, which on behalf of “the Bank” asked to provide information on the payment card or username/password from web banking, which are necessary for payment.